Case Study – Insurance
The client in question required a secure method to collect and store credit card information obtained from customers through their call centers. Subsequently, this information, along with customer data, needed to be transmitted to their designated Payment Gateway to finalize the transaction. Notably, the client operated with a distinct merchant account for each of their call center sites, totaling seven different gateway merchant accounts that required configuration. Additionally, they needed the capability to select the relevant merchant account for each API request sent.
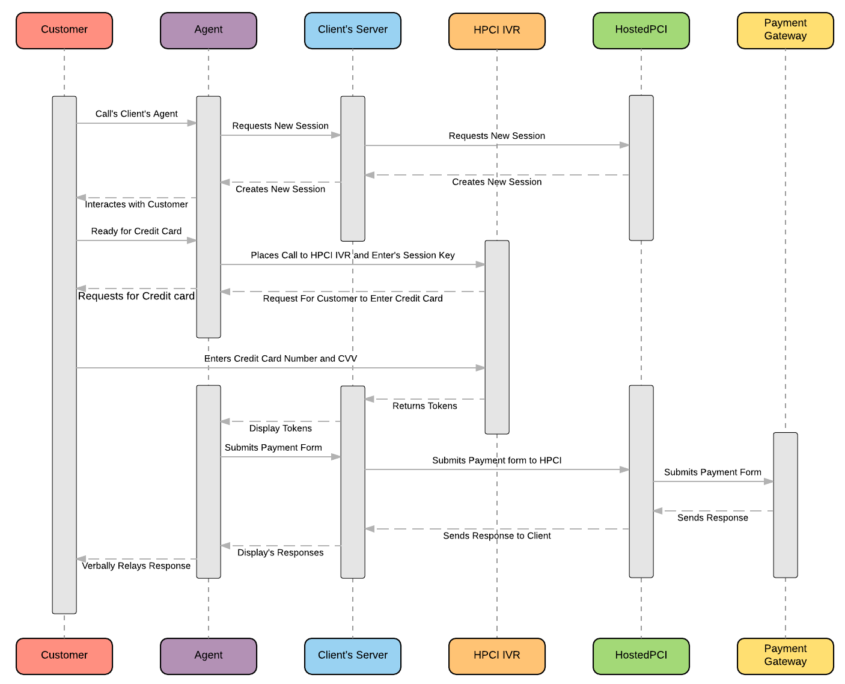
Our initial step involved identifying the most suitable collection method for the client. Given their preference for a secure method to collect credit card data from call centers, we determined that our Interactive Voice Response (IVR) solution was the optimal choice. This solution was particularly fitting as it is user-friendly while preserving customer experience. The HostedPCI IVR facilitates a three-way call involving the customer, the agent, and our IVR system. As customers input their credit card information using DTMF tones, agents are available to provide guidance if needed. To ensure the agent is outside the PCI scope, HostedPCI introduces additional tones to the credit card DTMF string, resulting in a total of 20 – 24 digits. Integrated directly with our Payment Vault, the tokenized credit cards are securely stored, and the client is furnished with a reusable token for any third party.
The client’s requirement to select a specific merchant account for each API request was addressed by configuring seven different gateway merchant accounts, each corresponding to a call center site.
HostedPCI’s tokenization solution offers remarkable flexibility, allowing clients to select from a range of number combinations for tokenization. In this case, the client opted for a 1+11+4 combination, preserving the first and last four digits of the credit card number while tokenizing the intervening eleven digits. This transformation renders the data non-sensitive, as the tokenized 16-digit number bears no resemblance to any actual credit card number, thereby safeguarding it against breaches.
Upon collecting the credit card information via HostedPCI IVR, the client can formulate a real-time API AUTH request and proceed with a capture following the gateway’s completion of fraud checks. During the construction of the API request, a specific parameter, the PayName, is utilized to pinpoint the exact merchant account necessary for the transactions in question.
By adopting this approach, the client successfully minimized their PCI scope. The entire procedure of data collection, storage, and transfer was shifted to a secure third-party proxy, effectively reducing their PCI scope from a meticulous SAQ Type D, involving around four hundred questions, to a more manageable SAQ Type A, consisting of approximately eleven questions.