Payment Tokenization Explained: How Businesses Store Credit Cards Without Storing Card Data
Businesses today rely heavily on stored payment information. Subscription services, SaaS platforms, healthcare providers, travel companies, and many other organizations need the ability to securely store customer payment details for recurring billing and future transactions.
However, storing credit card numbers directly creates serious security risks and dramatically increases PCI DSS compliance requirements.
Payment tokenization solves this challenge.
By replacing sensitive cardholder data with a secure token, businesses can store and use payment information without exposing actual card numbers within their environment.
Understanding how tokenization works can help businesses improve security, simplify PCI compliance, and gain greater flexibility in their payment infrastructure.
What Is Payment Tokenization?
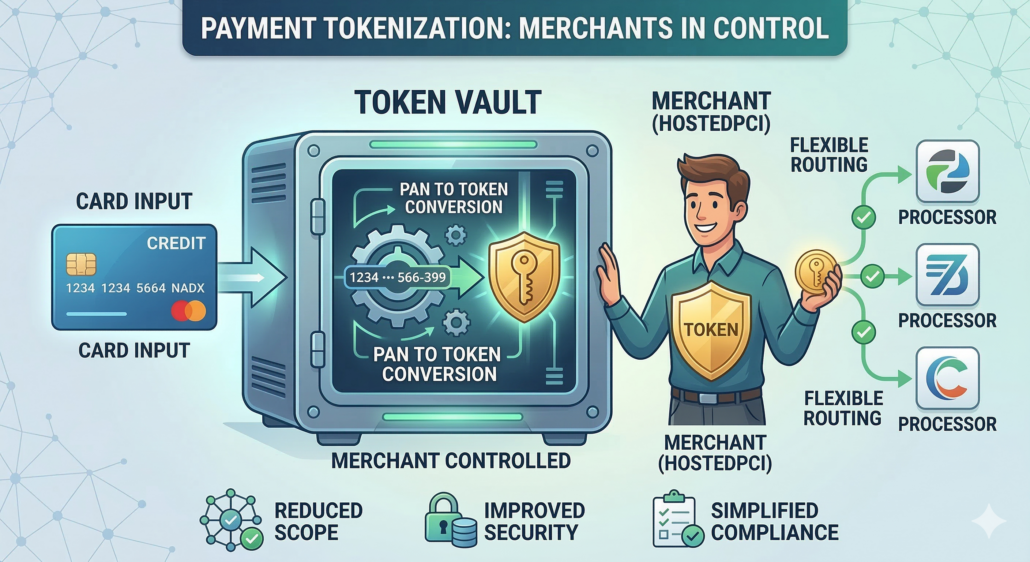
Payment tokenization is a security process that replaces a credit card number (PAN) with a randomly generated identifier known as a token.
The token represents the card but has no exploitable value outside the secure token vault where it was created.
Instead of storing the actual credit card number, businesses store the token. When a payment needs to be processed, the token is sent to the secure vault, where the real card number is retrieved and transmitted to the payment processor.
Because the merchant system never stores or directly handles the card number, the risk of data exposure is significantly reduced.
Tokenization is widely used in:
- Subscription billing platforms
- E-commerce checkout systems
- Mobile applications
- Call centers accepting payments over the phone
- Customer vaults for stored payment methods
For businesses that rely on stored payment data, tokenization has become a core security practice.
Why Storing Card Data Creates PCI Scope
The Payment Card Industry Data Security Standard (PCI DSS) requires businesses that store, process, or transmit cardholder data to follow strict security controls.
If a business stores raw credit card numbers within its systems, it must secure:
- Databases containing card data
- Servers that process transactions
- Network infrastructure handling payment traffic
- Access controls and monitoring systems
- Security audits and annual compliance validation
This can create significant operational overhead and security risk.
Tokenization helps reduce this burden by keeping cardholder data outside the merchant environment. Instead of protecting sensitive card numbers internally, businesses store only tokens, which have no usable value if exposed.
This dramatically reduces the number of systems that fall within PCI scope.
Tokenization vs Encryption
Tokenization and encryption are often confused, but they serve different purposes.
Encryption protects data by converting it into an unreadable format that can later be decrypted using a key. If an attacker gains access to both the encrypted data and the key, the original data can potentially be recovered.
Tokenization, on the other hand, replaces sensitive data with a non-sensitive reference value.
The token itself has no mathematical relationship to the original card number and cannot be reversed to reveal the underlying data. Only the secure token vault can map the token back to the original card information.
Because tokens cannot be reverse-engineered, they offer a powerful way to limit exposure to sensitive cardholder data.
Gateway Tokens vs Merchant-Controlled Tokens
Not all tokenization solutions are the same.
Many payment gateways generate tokens that only work within their own platform. These gateway-specific tokens allow businesses to process payments through that gateway, but the tokens cannot be used with other processors.
This creates a form of vendor lock-in.
If a business wants to change processors or add redundancy, the stored tokens may not be usable with a new provider. In some cases, merchants must ask customers to re-enter their card details or perform complex data migration processes.
Merchant-controlled tokenization provides a more flexible approach.
With merchant-controlled tokens, the business owns the tokens and can use them across multiple payment gateways and processors. This allows companies to maintain control over their payment infrastructure while still benefiting from tokenized security.
Why Token Ownership Matters
Token ownership can have a significant impact on a business’s long-term payment strategy.
When merchants control their tokens, they gain several advantages
Processor Flexibility
Businesses can route payments through multiple gateways or switch processors without losing stored payment data.
Redundancy and reliability
If one processor experiences downtime or service disruptions, transactions can be routed through an alternative provider.
Better pricing leverage
Merchants are not locked into a single processor and can negotiate better transaction rates.
Future-proof infrastructure
As payment technology evolves, businesses can integrate new processors and services without forcing customers to re-enter their payment information.
For companies managing large customer bases or recurring payments, this flexibility can be extremely valuable.
How Tokenization Helps Reduce PCI Scope
One of the primary reasons businesses adopt tokenization is to reduce their PCI compliance burden.
When implemented correctly, tokenization removes sensitive cardholder data from the merchant environment. Instead of storing credit card numbers, businesses store tokens that reference secure data held within a compliant vault.
This means fewer internal systems need to meet PCI DSS requirements.
Reducing PCI scope can lead to:
- Lower compliance costs
- Simpler security architecture
- Reduced risk of cardholder data exposure
- Easier PCI assessments
While tokenization does not eliminate PCI obligations, it can significantly reduce the systems that require strict security controls.
How HostedPCI Helps Businesses Secure Payment Data
HostedPCI provides tokenization and secure payment data storage designed to help businesses reduce PCI scope while maintaining control over their payment infrastructure.
Through secure tokenization and HostedPCI’s Transparent Data Flow architecture, sensitive cardholder data is captured and stored outside the merchant environment. Businesses can store tokens instead of raw card numbers while maintaining the ability to process transactions across multiple gateways.
This approach allows companies to:
- Store payment methods securely
- Reduce PCI scope
- Maintain processor flexibility
- Support recurring billing and stored credentials
- Avoid vendor lock-in
For organizations managing subscription billing, customer vaults, or large volumes of stored payment data, tokenization provides both security and operational flexibility.
Payment tokenization has become an essential security strategy for businesses that store customer payment information.
By replacing sensitive card numbers with secure tokens, companies can protect customer data, reduce PCI compliance scope, and maintain flexible payment processing options.
As payment environments become more complex, having control over tokenized payment data can help businesses scale securely while avoiding long-term infrastructure limitations.
Businesses that rely on stored payment methods should evaluate whether their current tokenization approach provides the security, flexibility, and processor independence needed for the future.
HostedPCI helps businesses tokenize, store, and manage payment data securely while maintaining control over their payment infrastructure.
To learn how tokenization can reduce PCI scope and improve payment flexibility, businesses can explore HostedPCI’s secure payment data storage solutions.
Learn more at www.hostedpci.com.